Mar 12, 2013 John the Ripper adalah suatu program yang lumayan terkenal di dunia hacking. JTR biasa digunakan untuk meng-Crack suatu password. INSTALASI JOHN THE RIPPER - Download John the Ripper 1.7.0.1 (Windows – binaries, ZIP, 1360 KB) klik DISINI Beberapa tips yg akan mempermudah saat menginstal John the Ripper pada windows 1. Cracking Password menggunakan John the Ripper pada Linux – Halo semuanya, kali ini Admin S akan membahas perihal cracking password menggunakan john Cara Install Web Server Apache di Debian 10 Linux June 4, 2020.
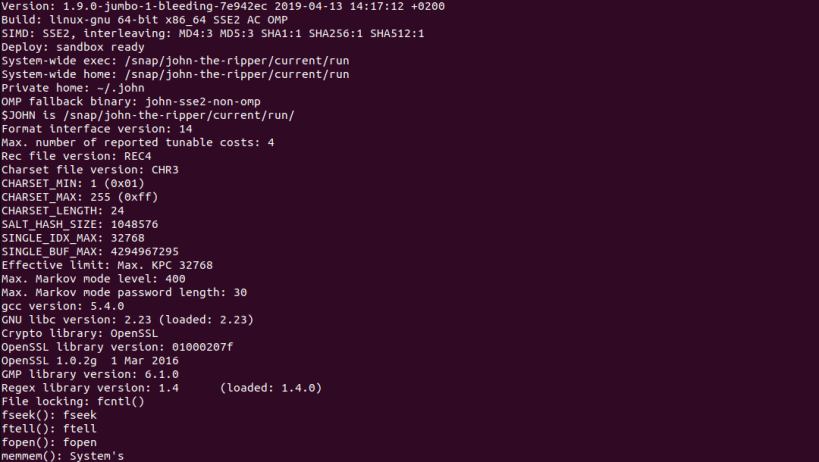
Install John The Ripper Password Cracker Versi Komunitas di Linux Software John The Ripper biasanya digunakan untuk memecahkan linux y windows. Tutorial John The Ripper Kita akan menggunakan cara kuno untuk mendapatkan password root dan seluruh password user yang ada di sebuah shell, disini penulis menggunakan. Cara Install John The Ripper Di Windows 10 Free This version integrates lots of contributed patches, including GPU support,dynamic expressions, has fallback for CPU SIMD extensions and for OMP,moreover, has on device mask acceleration and prince mode available. Cara Install John The Ripper Di Windows 10 Vw Touareg Navigation Rns2 Cd Download. Wilcom EmbroideryStudio is suitable for 32-bit versions of Windows XP/7/8/10.
|
Installing John the Ripper.
First of all, most likely you do not need to install John the Rippersystem-wide. Instead, after you extract the distribution archive andpossibly compile the source code (see below), you may simply enter the'run' directory and invoke John from there.
System-wide installation is also supported, but it is intended for useby packagers of John for *BSD 'ports', Linux distributions, etc., ratherthan by end-users. (If you're in fact preparing a package of John,please refer to the JOHN_SYSTEMWIDE setting in src/params.h.)
You may have obtained the source code or a 'binary' (pre-compiled)distribution of John the Ripper. On Unix-like systems, it is typicalto get the source code and compile it into 'binary' executables righton the system you intend to run John on. On DOS and Windows, however,it is typical to get a binary distribution which is ready for use.
The following instructions apply to the source code distribution ofJohn only. If you have a binary distribution, then there's nothingfor you to compile and you can start using John right away.
Compiling the sources on a Unix-like system.
Enter the directory into which you extracted the source codedistribution of John. Enter the 'src' subdirectory and invoke 'make'to obtain a list of operating systems for which specific supportexists:
Note the make target for your system and type:
where SYSTEM is the appropriate make target. Alternatively, if yoursystem is not listed, use:
If everything goes well, this will create the executables for John andits related utilities under './run/'. You can change directory tothere and start John, like this:
Alternatively, you may copy the entire 'run' directory to anywhere youlike and use John from there.
A note on moving binaries between systems.
With the 'generic' make target, certain machine hardware performanceparameters are detected at compile time. Additionally, some OS-specificmake targets tell the C compiler to generate and optimize code for themachine's specific CPU type (this currently applies to C compilers otherthan gcc only). If you then move the binary executable to a differentmachine, you might not get the best performance or the program mightnot run at all if the CPU lacks features that the C compiler assumed itwould have. Thus, it is recommended to recompile John on each system ifyou use one of these make targets.
Since Linux and *BSD distributions' packages of John typically use maketargets other than 'generic' and since they typically use gcc, they areusually not affected by this potential problem.
$Owl: Owl/packages/john/john/doc/INSTALL,v 1.5 2010/05/27 13:37:48 solar Exp $
Sumber: http://kalilinuxcourse.blogspot.co.id/2015/10/crack-password-using-kali-linux-2.0.html
- 3Tool yang digunakan untuk Password Cracking
- 3.2Hack Password Menggunakan Pyrit
Password Attack
Password Cracking adalah proses menyerang password dari data yang telah tersimpan atau dikirim oleh sistem komputer. Pendekatan yang umum digunakan adalah brute force attack dengan cara berulang kali mencoba menebak password.
Tujuan cracking password mungkin untuk membantu pengguna memulihkan password yang lupa (walaupun menginstal password yang sama sekali baru akan mengurangi dari risiko keamanan, namun melibatkan hak istimewa sebagai Sistem Administrator), untuk mendapatkan akses tidak sah ke sistem, atau sebagai tindakan pencegahan oleh Administrator Sistem untuk memeriksa password yang mudah rusak. Secara file-by-file, cracking password digunakan untuk mendapatkan akses ke bukti digital dimana hakim mengizinkan akses namun akses file tertentu dibatasi.
Programmer komputer telah mencoba membuat algoritma untuk memecahkan password dalam waktu yang lebih singkat. Sebagian besar tool cracking password mencoba masuk dengan setiap kemungkinan kombinasi kata-kata. Jika login berhasil, berarti password sudah ditemukan. Jika password cukup kuat dengan kombinasi angka, karakter dan karakter khusus, metode cracking ini mungkin memakan waktu berjam-jam sampai berminggu-minggu atau berbulan-bulan. Beberapa tool cracking password menggunakan kamus yang berisi kata sandi. Tool ini sangat bergantung pada kamus, jadi tingkat keberhasilannya lebih rendah.
Tips untuk membuat Password yang kuat
Semakin panjang password, semakin sulit di crack: Panjang password adalah faktor yang paling penting. Jika anda memilih password pendek, tool cracking password dapat dengan mudah memecahkannya dengan menggunakan beberapa kombinasi kata. Password yang lebih panjang akan memakan waktu lebih lama untuk menebak. Password Anda harus minimal 8 karakter.
Selalu gunakan kombinasi karakter, angka dan karakter khusus: Ini adalah hal lain yang membuat password sulit dipecahkan. Tool cracking password mencoba kombinasi satu per satu. Memiliki kombinasi karakter kecil, huruf kapital, dan karakter khusus. Misalkan jika anda hanya memiliki angka dalam password anda. Tool cracking password hanya perlu menebak angka dari 0-9. Disini hanya panjang password yang menjadi penentu. Tapi memiliki kombinasi kata kunci a-z, A-Z, 0-9 dan karakter spesial lainnya yang cukup panjang akan membuat lebih sulit untuk di crack. Password semacam ini terkadang memakan waktu berminggu-minggu untuk dipecahkan.
Keragaman dalam password: Satu hal penting yang harus selalu Anda jaga. Jangan pernah menggunakan kata sandi yang sama di mana saja. Penjahat cyber bisa mencuri password dari satu situs web dan kemudian mencobanya di situs lain-nya.
Contoh strong password: AdZfL48024@ #$!
Tool yang digunakan untuk Password Cracking
- GPU Tools
- Online Attack
- Offline Attack
- Passing The Hash
GPU Tools
GPU, atau unit pemrosesan grafik, digunakan terutama untuk aplikasi 3-D. Ini adalah prosesor chip tunggal yang menciptakan efek pencahayaan dan men-transformasi objek setiap kali 3D scene digambar ulang. Ini adalah tugas-tugas yang intensif secara matematis, yang akan cukup membebani CPU. Memindahkan beban ini dari CPU akan membebaskan siklus CPU digunakan untuk pekerjaan lain.
Alasan sederhana dalam menggunakan GPU daripada CPU untuk memecahkan password adalah karena GPU lebih cepat. Ternyata cracking passwords sangat mirip dengan Bitcoin mining, jadi alasan yang sama GPU lebih cepat untuk Bitcoin mining berlaku untuk cracking password. Jawaban singkatnya adalah bahwa ada banyak chip khusus pada GPU yang melakukan operasi 32-bit dengan sangat cepat. Meskipun CPU dapat melakukan banyak perhitungan untuk keperluan umum, chip pada GPU dapat melakukan jenis operasi tertentu lebih cepat, dan dengan cara lebih mem-paralel-kan proses.
Hack Password Menggunakan Pyrit
Step 1:
Set Wi-Fi menjadi mode monitor dengan airmon-ng. Buka terminal dan ketik:
Catatan: airmon-ng akan me-rename wlan0 menjadi mon0.
Step 2:
Capture Traffic menggunakan airodump-ng. Ini akan menangkap traffic dan menampilkan informasi seperti, BSSID (AP MAC address), power, jumlah beacon frame, jumlah data frame, channel, speed, encryption (if any), dan juga, ESSID (biasanya kita mengenalkan sebagai SSID). Ketik:

Semua AP yang terlihat akan tampil di bagian atas layar, client akan berada di bagian bawah layar.
Step 3:
Menggunakan airodump-ng menangkap Handshake. Langkah ini adalah memfokuskan usaha kita pada satu AP pada satu channel, dan menangkap data penting dari AP tersebut. Kita perlu men-set BSSID dan channel untuk itu. Ketik pada terminal,
Dimana
- 08:86:30:74:22:76 adalah AP BSSID
- -c 6 adalah channel dimana AP beroperasi
- WPAcrack adalah nama file untuk menyimpan hasil
- mon0 adalah adapter wifi yang memonitor jaringan
Catatan: paling asik kalau kita bisa memperoleh AP yang konfigurasi-nya default tidak diubah oleh user.
Step 4:
Aireplay-Ng Deauth
Untuk mendapatkan password yang dienkripsi, kita harus meminta klien untuk melakukan otentikasi terhadap AP. Jika sudah diautentikasi, kami dapat membatalkan otentikasi (kick off) dan sistem mereka akan secara otomatis mengautentikasi ulang, di mana kita dapat mengambil password terenkripsi mereka dari proses tersebut.
Buka terminal baru, ketik:
Setelah berhasil menangkap handshake, gunakan pyrit untuk crack wifi password.
Steps To Use Pyrit To Crack Password
1. svn checkout http://pyrit.googlecode.com/svn/trunk/ pyrit_svn
Download the pyrit file
2. cd pyrit_svn/pyrit/ ./setup.py build install
Build and install setup.py file
3. cd .
Step back to pyrit_svn4. cd cpyrit_calpp
Go to cpyrit_calpp directory
5. Edit setup.py and find VERSION = '0.4.0-dev and change to VERSION = '0.4.1-dev
also find CALPP_INC_DIRS.append(os.path.join(CALPP_INC_DIR, 'include')) and replace with CALPP_INC_DIRS.append(os.path.join(CALPP_INC_DIR, 'include/CAL'))
Save the file
6. ./setup.py build install
Build and install and edited file
7. pyrit –e MTNL create_essid
Create essid in pyrit databases
8. pyrit -i wordlist .lst import_passwords
Import the dictionary in pyrit databases
9. pyrit batch
Create table in pyrit databases
10.pyrit –r MTNL .cap attack_db
Perform attack on handshake file
Offline Attack
Cmospwd
CmosPwd is a cross-platform tool to decrypt password stored in CMOS used to access a computer’s BIOS setup.
Crunch
Crunch is a wordlist generator where you can specify a standard character set or a character set you specify. crunch can generate all possible combinations and permutations.
Solidworks 2005 torrent crack mac. Generate a dictionary file containing words with a minimum and maximum length of 6 (6 6) using the given characters (0123456789abcdef), saving the output to a file (-0 6chars.txt):
hash-identifier
Software to identify the different types of hashes used to encrypt data and especially passwords.
John the Ripper
John the Ripper is another well-known free open source password cracking tool for Linux, Unix and Mac OS X. A Windows version is also available. This tool can detect weak passwords. A pro version of the tool is also available, which offers better features and native packages for target operating systems. You can also download Openwall GNU/*/Linux that comes with John the Riper.
Combine the provided passwd (passwd) and shadow (shadow)(shadow) and redirect them to a file (> unshadowed.txt):
Using a wordlist (–wordlist=/usr/share/john/password.lst),
apply mangling rules (–rules) and attempt to crack the password hashes in the given file (unshadowed.txt):
johnny
Johnny provides a GUI for the John the Ripper password cracking tool. Sankat mochan mahabali hanuman sony tv serial song download.
RainbowCrack
RainbowCrack is a hash cracker tool that uses a large-scale time-memory trade off process for faster password cracking than traditional brute force tools. Time-memory trade off is a computational process in which all plain text and hash pairs are calculated by using a selected hash algorithm. After computation, results are stored in the rainbow table. This process is very time consuming. But, once the table is ready, it can crack a password must faster than brute force tools.
You also do not need to generate rainbow tablets by yourselves. Developers of RainbowCrack have also generated LM rainbow tables, NTLM rainbow tables, MD5 rainbow tables and Sha1 rainbow tables. Like RainbowCrack, these tables are also available for free. You can download these tables and use for your password cracking processes.
This tool is available for both Windows and Linux systems.

rcracki-mt
rcracki_mt is a modified version of rcrack which supports hybrid and indexed tables. In addition to that, it also adds multi-core support.
Crack the password hash (-h 5d41402abc4b2a76b9719d911017c592) using 4 CPU cores (-t 4) and the specified rainbow tables (tables2/md5/):
RSMangler
RSMangler will take a wordlist and perform various manipulations on it similar to those done by John the Ripper the main difference being that it will first take the input words and generate all permutations and the acronym of the words (in order they appear in the file) before it applies the rest of the mangles.
Use the original wordlist (cat words.txt |) and mangle words with a minimum length of 6 (-m 6) and maximum length of 8 (-x 8), using stdin as input (–file -) and redirecting the results to a new wordlist (> mangled.txt): root@kali:~# cat words.txt | rsmangler -m 6 -x 8 --file - > mangled.txt
TrueCrack
TrueCrack is able to perform a brute-force attack based on:
Dictionary: read the passwords from a file of words.
Alphabet: generate all passwords of given length from given alphabet.
TrueCrack works on gpu and cpu
cachedumpIt is used to recover the windows password using cached entries.
CacheDump will create a CacheDump NT Service to get SYSTEM right and make his stuff on the registry. Then, it will retrieve the LSA Cipher Key to decrypt (rc4/hmac_md5 GloubiBoulga) cache entries values. A John The Ripper module has been developed to attack the hashed values that are retrieved
chntpw
It is used to Removing Windows OS Passwords.
So Lets' get started:
Step 1: Mounting the drive containing Windows OS-> This one is easy ain't it? Well so that you might not have forgotten how to do it, I'll type the syntax:
Note that 'sda1' in above command is the partition on which Windows OS is installed yours can be different. To check yours simply type fdisk -l which will list your all partitions and then check by yourself on which partition your Windows OS is installed.
Step 2: Now move to the config folder of windows os using below command:
Step 3:Type the following command to see the list of users available on Victim's Machine:
Step 4:Copy the name of user whose password you want to crack and then enter the below command to crack the password of selected user:
dictstat
It is used to Generate dictionary file statistics

fcrackzip
fcrackzip is a fast password cracker partly written in assembler. It is able to crack password protected zip files with brute force or dictionary based attacks.
1.Open Terminal type fcrackzip –help this command will open fcrackzip with help options
2. Let’s make a zip file in windows 7 PC than we will copy paste it into Kali Linux afterthat we will try to break this password by fcrackzip. I created a zip file. This zip file’s password is 12345678.
3. Now we are going to break this password protected zip file. If you know your password has numeric (ex- 123.) and how many digits there in your password. Here we know our password is numeric (e.g. 123…) and its total 8 digits. If you have just small thought or knowledge about your password It will you to speed up your brute force attack against your zip file.
Syntax – fcrackzip –u –c <your password character type> –p <total digits> zip file path
Here,
The –u option, Try to decompress the first file by calling unzip with the guessed password. This weeds out false positives when not enough files have been given.
The –c option lets you select the character set, '1' here means password can be a numeric.
The -p option lets you select an initial string to start brute-force attack
Note – as you can see I wrote ‘aaaaaaaa’, if you will count this is total 8 digits means I assumed that my password can be 8 digits but in this step if my assumption will be wrong, like my password have 8 digits and I will write there ‘aaaaaaa’ (only 7 digits) than fcrackzip will not crack your password.
4. If you know your password is numeric but you don’t know there are how many digits. You can assume a password digit range. Here I am thinking that my password can be minimum 4 digits to maximum 8 digits.
Syntax – fcrackzip –u –c <your password character type> -l <password digits range> zip file path
5. In this Example I created another Zip file with small (lower case) alphabet digits as password. Here password is ‘abcdefgh’. If your password has small alphabets characters and length of password is 8 digits.
Syntax – fcrackzip –u –c <your password character type> –p <total digits> zip file path
Here we are using ‘a’ after –c because our password has small (lower case) alphabet. If you have doubt that the password can be capital (upper case) alphabet than you have to write capital ‘A’. If you think that your password has both upper and lower case than you can write ‘Aa’. Just like this if you doubt your password has lower case (a), Upper case (A), numeric (1). You have to write there ‘Aa1’.
6. Range of password digits
7. Here we are using brute force a zip file password which has upper case (A), lower case (a), numeric (1), and symbol (@). Use '!' for including special characters !:$%&/()=?{[]}+*~#. If you want to specify only some of the characters then mention them using ' : '. In this image I want to specify only one (@) character so I used :@.
8. Now we are going to crack this zip password by using dictionary attack. Just for an example I am making a small dictionary manually so it will take less time to crack.
9. Now run the command for cracking this zip file password
Syntax – fcrackzip –u –D –p <dictionary file path> <zip file path>
hashcat
It is a CPU-based password recovery tool.Hashcat or cudaHashcat is the self-proclaimed world’s fastest CPU-based password recovery tool. Versions are available for Linux, OSX, and Windows and can come in CPU-based or GPU-based variants. Hashcat or cudaHashcat currently supports a large range of hashing algorithms, including: Microsoft LM Hashes, MD4, MD5, SHA-family, Unix Crypt formats, MySQL, Cisco PIX, and many others.
md5.txt : File in which hashed password is saved
/root/rockyou.txt : path of dictionery file which used to crack hashed password
hashid
Identify the different types of hashes used to encrypt data and especially passwords.
maskgen
Generate hashcat masks
opcrack
A Microsoft Windows password cracker using rainbow tables
Ophcrack uses Rainbow Tables to crack NTLM and LM hashes into plain text, its a free Windows password cracker based on rainbow tables. It is a very efficient implementation of rainbow tables done by the inventors of the method. If you have a complex password it will take a lot longer than simple passwords, and with the free tables your password may never be cracked.
sipcrack
SIPcrack is a SIP login sniffer/cracker that contains 2 programs: sipdump to capture the digest authentication and sipcrack to bruteforce the hash using a wordlist or standard input.
sipcrack bruteforces the user’s password with the dump file generated by sipdump. If a password is found, the sniffed and cracked login will be updated in the dump file.
Cara Install John The Ripper Di Windows 10 Pro
Sipcrack needs a wordlist to launch an attack. As a result, it will give you the password.
sucrack
Multithreaded Linux/UNIX tool for brute-force cracking of local user accounts via su.
Online Attack
acccheck
The tool is designed as a password dictionary attack tool that targets windows authentication via the SMB protocol. It is really a wrapper script around the ‘smbclient’ binary, and as a result is dependent on it for its execution.Scan the IP addresses contained in smb-ips.txt (-T) and use verbose output (-v):
Burp Suite
Burp Suite is an integrated platform for performing security testing of web applications. Its various tools work seamlessly together to support the entire testing process, from initial mapping and analysis of an application’s attack surface, through to finding and exploiting security vulnerabilities.
Burp gives you full control, letting you combine advanced manual techniques with state-of-the-art automation, to make your work faster, more effective, and more fun.
CeWL
CeWL is a ruby app which spiders a given url to a specified depth, optionally following external links, and returns a list of words which can then be used for password crackers such as John the Ripper.
CeWL also has an associated command line app, FAB (Files Already Bagged) which uses the same meta data extraction techniques to create author/creator lists from already downloaded.
Scan to a depth of 2 (-d 2) and use a minimum word length of 5 (-m 5), save the words to a file (-w docswords.txt), targeting the given URL
Cisco-Auditing-ToolPerl script which scans cisco routers for common vulnerabilities.
Scan the host (-h 192.168.99.230) on port 23 (-p 23), using a password dictionary file (-a /usr/share/wordlists/nmap.lst):
DBPwAudit
DBPwAudit is a Java tool that allows you to perform online audits of password quality for several database engines. The application design allows for easy adding of additional database drivers by simply copying new JDBC drivers to the jdbc directory. Configuration is performed in two files, the aliases.conf file is used to map drivers to aliases and the rules.conf tells the application how to handle error messages from the scan.
Scan the SQL server (-s 192.168.1.130), using the specified database (-d testdb) and driver (-D MySQL) using the root username (-U root) and password dictionary (-P /usr/share/wordlists/nmap.lst)
FindMyHash
It will crack hashes with online service.
Specifying the hash algorithm (MD5), attempt to crack the given hash (-h 098f6bcd4621d373cade4e832627b4f6)
THC-Hydra
Hydra is a parallelized login cracker which supports numerous protocols to attack. It is very fast and flexible, and new modules are easy to add. This tool makes it possible for researchers and security consultants to show how easy it would be to gain unauthorized access to a system remotely.
It supports: Cisco AAA, Cisco auth, Cisco enable, CVS, FTP, HTTP(S)-FORM-GET, HTTP(S)-FORM-POST, HTTP(S)-GET, HTTP(S)-HEAD, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MySQL, NNTP, Oracle Listener, Oracle SID, PC-Anywhere, PC-NFS, POP3, PostgreSQL, RDP, Rexec, Rlogin, Rsh, SIP, SMB(NT), SMTP, SMTP Enum, SNMP v1+v2+v3, SOCKS5, SSH (v1 and v2), SSHKEY, Subversion, Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP.
Attempt to login as the root user (-l root) using a password list (-P /usr/share/wordlists/metasploit/unix_passwords.txt) with 6 threads (-t 6) on the given SSH server (ssh://192.168.1.123):
root@kali:~# hydra -l root -P /usr/share/wordlists/metasploit/unix_passwords.txt -t 6 ssh://192.168.1.123
Keimpx
keimpx is an open source tool, released under a modified version of Apache License 1.1.
It can be used to quickly check for valid credentials across a network over SMB. Credentials can be:
NcrackNcrack is a high-speed network authentication cracking tool. It was built to help companies secure their networks by proactively testing all their hosts and networking devices for poor passwords. Security professionals also rely on Ncrack when auditing their clients. Ncrack was designed using a modular approach, a command-line syntax similar to Nmap and a dynamic engine that can adapt its behaviour based on network feedback. It allows for rapid, yet reliable large-scale auditing of multiple hosts.
Ncrack’s features include a very flexible interface granting the user full control of network operations, allowing for very sophisticated bruteforcing attacks, timing templates for ease of use, runtime interaction similar to Nmap’s and many more. Protocols supported include RDP, SSH, http(s), SMB, pop3(s), VNC, FTP, and telnet.
John The Ripper Github
Use verbose mode (-v), read a list of IP addresses (-iL win.txt), and attempt to login with the username victim (–user victim) along with the passwords in a dictionary (-P passes.txt) using the RDP protocol (-p rdp) with a one connection at a time (CL=1):
Patator
Patator is a multi-purpose brute-forcer, with a modular design and a flexible usage
Do a MySQL brute force attack (mysql_login) with the root user (user=root) and passwords contained in a file (password=FILE0 0=/root/passes.txt)against the given host (host=127.0.0.1), ignoring the specified string (-x ignore:fgrep=’Access denied for user’):
phrasendrescher
phrasen|drescher (p|d) is a modular and multi processing pass phrase cracking tool. It comes with a number of plugins but a simple plugin API allows an easy development of new plugins.
Use the SSH brute force plugin (ssh) and the passwords in a wordlist (-d passes.txt) against the target server (-t 192.168.1.202), displaying verbose output (-v):
THC-pptp-bruter
Brute force program against pptp vpn endpoints (tcp port 1723). Fully standalone. Supports latest MSChapV2 authentication. Tested against Windows and Cisco gateways. Exploits a weakness in Microsoft’s anti-brute force implementation which makes it possible to try 300 passwords the second.
WebScarab
WebScarab is designed to be a tool for anyone who needs to expose the workings of an HTTP(S) based application, whether to allow the developer to debug otherwise difficult problems, or to allow a security specialist to identify vulnerabilities in the way that the application has been designed or implemented.
- See more at: http://kalilinuxcourse.blogspot.co.id/2015/10/crack-password-using-kali-linux-2.0.html#sthash.9fAniGLD.dpuf